Email Security
Comprehensive & Accurate Email Protection
- Stop Attacks from Bad Actors – Securolytics leverages multiple Anti-virus engines as well as multiple feeds from both IP and Domain reputation services to identify known threats.
- Message Content Scanning – numerous spam filtering technologies provides content analysis and filtering
- Unmatched Accuracy – filter messaging threats with greater than 99% accuracy and near zero false positives, supporting all formats and languages, including languages using double-byte characters such as Japanese, Chinese and Cyrillic.
- Real-Time Response to Threats – Emails are analyzed, corroborated and threat protection is made available every 30 seconds. Fingerprinting technology tracks and identifies both conventional and mutating attacks.
- Broad Protection – complete inbound and outbound protection against all forms of messaging abuse including spam, phishing and malware attacks on fixed and mobile networks. There is no need to purchase, integrate or manage separate solutions for different types of threats.
- Stop Zero-Day Threats- file detonation and behavioral analysis identifies and blocks new threats as they emerge.
- Disaster Recovery Protection -automatically spool emails in case of unexpected events, so you never lose your business-critical email.
Make Encryption Easy on Users and on IT
- Transparent to Users – Securolytics’ unique “no log in” experience to recipients makes viewing encrypted email simple. And since users can both easily verify the sender and retrieve the message, it reduces workload and support issues with IT.
- Custom Branding- With your brand on the encrypted emails instead of ours, you can help to ensure your recipients that the email came from your organization.
- Ensure Recipients That Email Came From Your Organization – With Securolytics Click to Verify Authenticity, recipients can quickly verify that the email in fact came from your organization and that it was not spoofed.
- Flexible Enforcement – Choose to enforce encryption by keyword, content, DLP policy or on all email
Prevent Leakage of Sensitive Email Data
- Flexible Policy Definition – Choose to define policy by pre-defined lexicons like credit card, social security or bank or wire transfer numbers, PHI, credentials, etc., by sender or by custom strings, keywords or pattern matching.
- Flexible Trigger Actions- Pick to log only, quarantine, encrypt and send or reject emails that trigger a policy. Define the severity level of the trigger and automate email notifications.
- Support for SMTP, HTTP and FTP protocols
- Define the content that can be viewed in the management console by policy violation, the entire message or choose to show no content.
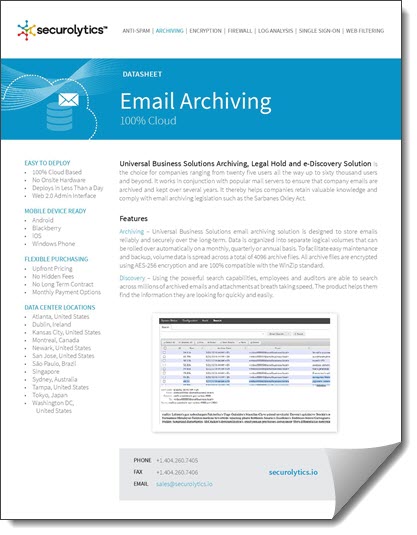
Meet Compliance and Discovery Requirements